Introduction
I Have Some Questions
Are you a member of your organization’s security or IT team? Good, keep reading, this guide was written for you. Are you an employee that works for an organization that is using security and IT management software? Good. Read this guide and find some members of your security team and share it with them.
In fact, before I start addressing the security team directly, I want to ask you, the employee (or end-user) some questions.
- When was the last time the security team gave you personalized advice?
- When was the last time the security team or even IT team asked for your permission before they made a change to your laptop?
- When was the last time the security team asked you for your thoughts on security risks you see in your daily workflow?
- Can you recall that time where they asked you how upcoming security changes to your device would impact your daily workflow?
Ok security teams, it is time for a reality check. As someone who has been in the security space for nearly a decade, I frequently chat with security and IT practitioners about their goals and objectives. Many teams describe themselves as an elite fighting squad working against shadowy forces who are trying to degrade, deny, and disrupt the key components of their organization. They adorn themselves with badges, flags, and other symbols associated with defenders and agents of authority. They firmly believe they are fighting the good fight, keeping the company’s interests safe, and protecting their end-users from compromise or incident. They are the good guys.
It’s always a surprise then that when I ask end-users the questions I posed earlier, the majority tell me the last time they talked with anyone from the security team was at a required annual training event. Some of them tell me they have never had a single one-on-one interaction with the security team. I’ve even met a few folks who have said their only interaction with the security team occurred when they clicked a link in a fake phishing simulation and were forced to take remedial training. They recalled how it made them feel humiliated. Others bemoaned the laggard performance of their once powerful laptops, rendered essentially unusable, because of all the numerous security agents running in the background. That person confided in me that she rarely uses her work computer and instead writes all her work emails from her personal iPad.
These are not the hallmarks of a healthy relationship.
The Tools Aren’t Helping
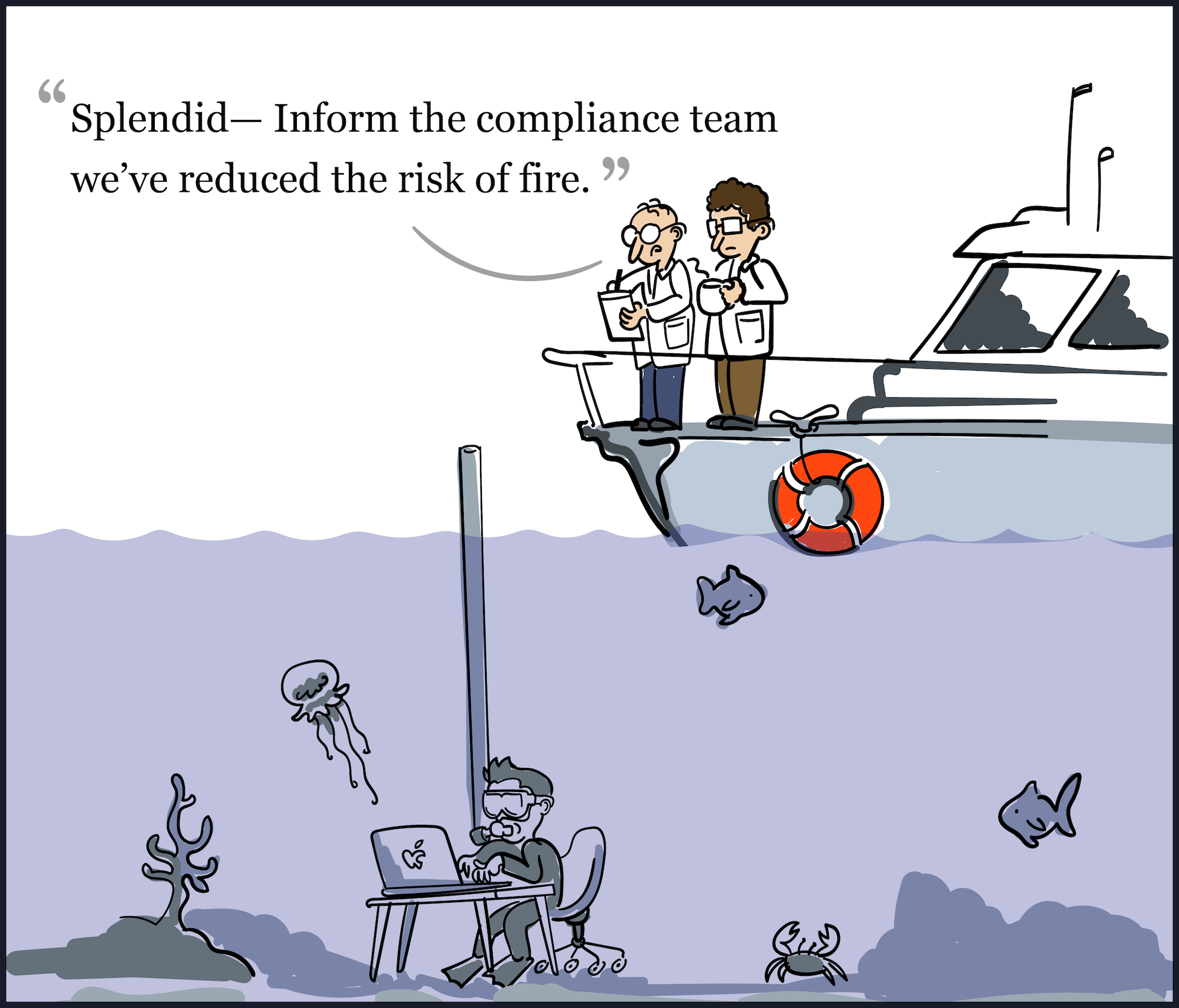
The products and applications which security teams use do not help improve this situation. Endpoint security is typically deployed under the cover of darkness where it remains mostly invisible to the end-user, persistently sapping the resources of the device for the benefit of the security team’s detection mission.
These endpoint agents run with administrative privileges and give security teams complete access to the device. They can download documents, view the web browser’s history, emit precise GPS coordinates of the device’s location, install software, and even erase all the files. These functions occur silently in the background at the behest of an administrator issuing commands remotely.
Our Personal Lives Are Inseparable from Our Devices
Did your company buy you a Mac? If yes, do me a favor and open up the Photos app. Are you immediately greeted by your friends and family? What about the Messages app? Are there any non-work conversations found there? If you answered yes, you join the 90% of people surveyed by Accenture in 2018 who also claimed to use their devices for personal activities. 55% surveyed went on to say that they have allowed either a friend or family member to use their laptop. These devices are not simply tools for work, they are portals into our personal lives.
Despite the sensitivity of this data, the end-user is not kept in the loop about what occurs under the hood of their device. Security teams do not have to provide ongoing and informed consent for any of the surveillance capabilities these tools employ. While the security team might be accountable to a third-party group, that group never includes the end-user who is essentially being surveilled.
Why This Guide Exists
I created this guide because I believe that a healthy working relationship with the end-user is an essential asset, necessary for every effective security team. And because our industry is so obsessed with creating tools focused only on extending visibility and increasing the security team’s control over the employee’s digital assets, this critical relationship is irreparably being destroyed.
It’s important for me to mention, not everyone has this wrong. In fact, there are dozens of security professionals whom I’ve spoken with that have healthy relationships with their end-users. The problem is that too few of them are talking about these loudly enough for others to hear. The approach of Honest Security is too important to be lost in the back-channel, so it is time to bring it forward where everyone can learn.
This guide is my attempt to codify the ideals and philosophies that we use as our north star at Kolide, a company dedicated to building products which foster this positive relationship. Some of the ideas presented here are a direct result of formative moments I experienced as an intelligence analyst at the GE CIRT. Other components are informed directly by my work developing many of the tools I deride in this guide in my role as Product Manager at Mandiant and Chief Security Strategist at FireEye. But much of the good stuff I didn’t think up on my own. All of the advice worth listening to in this guide was hard-won based on the work the team and I have been doing since 2019 at Kolide when we decided to shift our focus onto the end-user.
My hope is that by publishing this guide, we can generate an important discussion about the state of our industry which ultimately results in the adoption of these ideals by practitioners, tool makers, and even commercial vendors. One company in this space is better than zero, but it is not nearly enough.
A Quick Note about the Examples in This Guide
Many of the topics in this guide can feel abstract without concrete examples. As mentioned earlier, much of this guide is derived from the experiences and insights I’ve had working on our product at Kolide. This guide is aspirational (and our product is still missing some pieces), but I will use examples from Kolide to demonstrate ideas throughout relevant sections.
While I hope people who read this see the value in our product, my intent is not to turn this guide into a simple sales pitch. Please afford me the latitude to use examples from Kolide today, but also reach out and share other products (or even better, open source projects) that capture the spirit of the examples. I will gladly add them to this guide in a future revision.
